Telegram messages can be traced by police, but it requires advanced techniques and legal authority.
Introduction to Telegram and Privacy
Telegram, a widely used messaging app, is renowned for its strong emphasis on privacy and security. This section delves into the core elements of Telegram’s privacy features, focusing on its encryption methods and the legal and ethical implications surrounding messaging privacy.
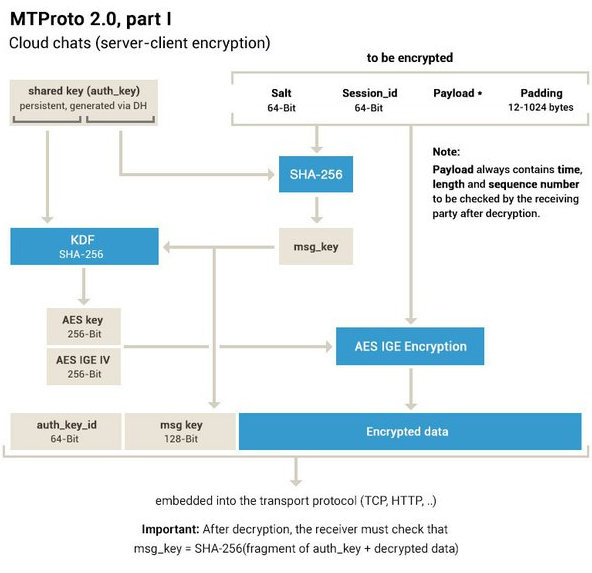
Overview of Telegram’s Encryption Methods
Telegram utilizes two distinct types of encryption: cloud-based encryption and end-to-end encryption. The cloud-based encryption is used in ‘Cloud Chats,’ which offers server-client encryption. This method ensures that messages are encrypted on the sender’s device and decrypted on the recipient’s device. Telegram maintains the encryption keys, which theoretically allows them to access message content.
Telegram’s ‘Secret Chats’ feature uses end-to-end encryption, ensuring that only the communicating users can read the messages. This method does not store the encryption keys on Telegram’s servers, making it impossible for the company to decrypt and read these messages.
Legal and Ethical Considerations in Messaging Privacy
The legal landscape for messaging apps like Telegram varies significantly across countries. In some regions, governments require companies to provide access to messages for law enforcement purposes. This raises critical questions about user privacy and the extent of government surveillance.
From an ethical standpoint, the debate centers on balancing national security interests with individual privacy rights. While law enforcement agencies argue that access to encrypted messages is crucial for preventing and investigating crimes, privacy advocates stress the importance of secure communication channels to protect users’ freedom of speech and prevent unwarranted government intrusion.
The use of encryption in Telegram has been a pivotal aspect in various high-profile cases, where the inability to access encrypted messages has both hindered criminal investigations and protected the privacy of individuals in sensitive political or social contexts.
These contrasting viewpoints highlight the complex interplay between privacy, security, and regulatory compliance in the digital age, placing messaging apps like Telegram at the center of a significant global debate.
Police Surveillance Techniques
The methods used by law enforcement agencies to trace messages and the international laws governing digital surveillance are critical to understanding the balance between security and privacy.
Methods Used by Law Enforcement to Trace Messages
Law enforcement agencies employ a range of techniques to trace messages, particularly in the context of criminal investigations. Network analysis is a primary method, involving the tracking of IP addresses and server logs to determine the source of a message. legal warrants can compel service providers to release user data. In some cases, agencies use advanced software tools to intercept or retrieve messages, which may involve exploiting security vulnerabilities.
Another notable method is social engineering, where investigators may use deception or manipulation to gain access to someone’s messages. This technique, though less technical, can be highly effective.
International Laws and Regulations on Digital Surveillance
Digital surveillance laws vary widely across the globe. In countries like the United States, the Electronic Communications Privacy Act (ECPA) and the Patriot Act provide a legal framework for digital surveillance. These laws allow for the collection of digital communication under specific circumstances, often requiring a court order.
The European Union’s General Data Protection Regulation (GDPR) places stricter controls on digital surveillance, emphasizing user privacy and consent. The GDPR imposes significant penalties for non-compliance, ensuring a higher standard of user data protection.
The table below highlights the differences between these two approaches:
| Aspect | United States (ECPA, Patriot Act) | European Union (GDPR) |
|---|---|---|
| Legal Requirements | Court orders required for surveillance; broader scope for authorities | Strict compliance, with emphasis on user consent and data protection |
| Data Protection | Less stringent, focuses on national security | High priority on data protection and privacy |
| Surveillance Scope | Relatively broad, with a focus on counter-terrorism | More restricted, with a strong emphasis on individual rights |
| Penalties for Breach | Varies depending on the severity of the breach | Severe financial penalties for non-compliance |
These contrasting approaches reflect the ongoing global debate on the balance between privacy and security in the digital era. While the United States tends to prioritize national security, the European Union leans more towards protecting individual privacy rights.
Case Studies: Telegram in Law Enforcement
Exploring historical instances of police tracing Telegram messages and analyzing legal precedents provides insight into the complex interplay between privacy, technology, and law.
Historical Instances of Police Tracing Telegram Messages
In various instances, law enforcement agencies have successfully traced Telegram messages, often in cases involving serious criminal activities,in 2016, German police managed to trace Telegram messages linked to a planned terrorist attack. This was achieved through network analysis and tracking IP addresses, despite Telegram’s robust encryption.
Another notable case occurred in Russia in 2018, where authorities claimed to have decrypted some Telegram messages related to a corruption investigation. However, the specifics of how this was achieved remain unclear, raising questions about whether vulnerabilities in Telegram’s system were exploited or if other methods were used.
These cases demonstrate that while Telegram offers high levels of encryption, determined efforts by law enforcement can sometimes lead to the tracing of messages, especially when national security is at stake.
Legal Precedents and Court Rulings on Message Tracing
Legal precedents regarding message tracing vary significantly across jurisdictions. In the United States, the FBI vs. Apple encryption dispute set a notable precedent. Although not directly related to Telegram, this case highlighted the legal and ethical challenges in accessing encrypted messages. The court initially ordered Apple to assist the FBI in unlocking an iPhone, but the order was later withdrawn when the FBI accessed the device through a third party.
In the European context, the European Court of Human Rights has ruled on several cases related to privacy and surveillance. These rulings often emphasize the need to balance privacy rights with security concerns. For example, in cases involving terrorism, courts have sometimes leaned towards granting law enforcement broader surveillance powers.
How secure are Telegram messages?
Can police access Telegram messages without user consent?
Does Telegram cooperate with law enforcement requests?
What encryption method does Telegram use?