Yes, videos in Telegram can contain viruses if they embed malicious code or exploit software vulnerabilities.
Introduction
Overview of Telegram and Video Sharing
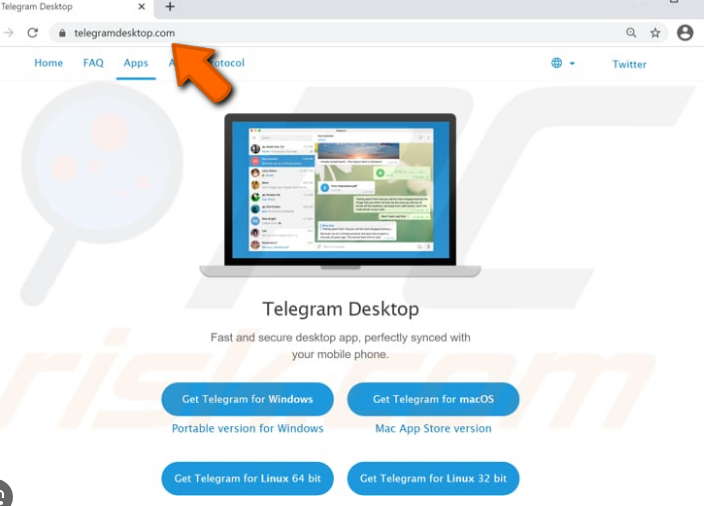
Telegram, a cloud-based messaging app, supports fast and secure messaging across a wide range of devices. It stands out for its ability to send large video files and media, with a current file sharing limit of up to 2GB per file. This makes it an ideal platform for sharing videos, whether for personal use or within large groups and channels. Telegram’s architecture ensures that media and messages are synchronized seamlessly across all user devices, offering a robust platform for video distribution.
Importance of Cybersecurity in Messaging Apps
In the digital age, cybersecurity in messaging apps has become paramount. With millions of users exchanging information daily, the potential for cyber threats escalates. Messaging apps, including Telegram, are not just platforms for communication but also for sharing sensitive data such as personal information, financial details, and private videos. Ensuring the security of these data exchanges is crucial to protect users from cyber threats, including viruses, malware, and phishing attacks. A strong emphasis on cybersecurity helps maintain user trust and prevents the exploitation of personal information.
Understanding the distinctions between various types of viruses and malware, as well as comprehending how these malicious entities can spread through videos, is essential for ensuring cybersecurity. Here’s a detailed overview in English, following your guidelines for structure and content specificity.
Understanding Viruses and Malware
Types of Viruses and Malware
Viruses and malware represent a significant threat to computer systems and personal data. Here’s a breakdown of the most common types:
| Type | Description | Propagation Method |
|---|---|---|
| Virus | Malicious software that needs to attach itself to a clean file and requires user action to spread. | Attachment to downloadable video files. |
| Worm | A self-replicating malware that spreads over networks without user interaction. | Exploits network vulnerabilities, possibly through video-sharing networks. |
| Trojan Horse | Disguised as legitimate software, it grants unauthorized access or harm to the user’s system. | Disguised in video files or related software downloads. |
| Adware/Spyware | Software that bombards with unwanted ads (Adware) or secretly collects data (Spyware). | Bundled with video player software downloads. |
| Ransomware | Encrypts the victim’s data, demanding payment for the decryption key. | Distributed via malicious video files leading to encryption upon download or opening. |
How Viruses Spread Through Videos
- Embedded Malicious Code: Viruses can be embedded directly into video files. When these videos are downloaded and played, the malicious code executes.
- Software Vulnerabilities: Attackers exploit vulnerabilities in video playback software or codecs, allowing them to execute malicious code when a video is played.
- Deceptive Downloads: Users may be tricked into downloading a video that is actually malware, often through misleading links or fake video descriptions.
This table highlights the diversity of malware and the various ways it can spread, particularly through video files, emphasizing the importance of maintaining up-to-date software and practicing cautious downloading habits.
Telegram’s Security Features
Telegram prides itself on offering robust security measures to protect its users’ data and privacy. Two key features underscore its commitment to security: End-to-End Encryption and Safe File Sharing Protocols.
Potential Risks of Video Files
The increasing use of video files as a means of communication and information sharing brings with it a unique set of cybersecurity risks. Two primary concerns are Embedded Viruses in Video Files and Exploits in Video Playback Software.
Embedded Viruses in Video Files
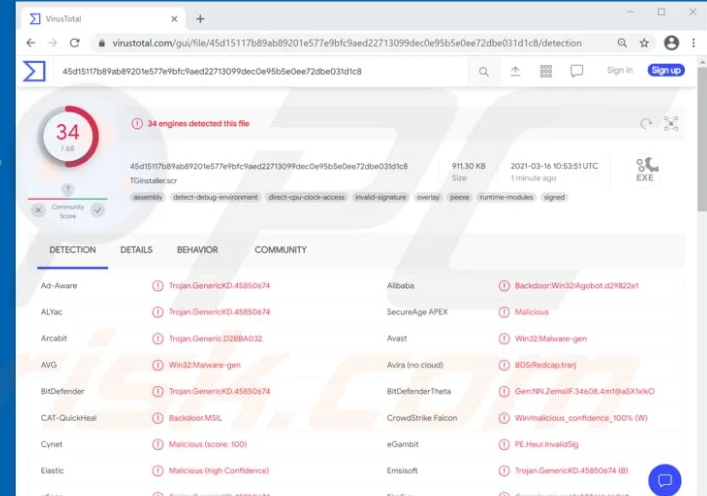
Cybercriminals can embed viruses directly into video files, a tactic that leverages the widespread sharing and downloading of videos. When unsuspecting users download and play these infected files, the embedded virus is executed, compromising the user’s system. This method of attack is particularly insidious because it exploits the trust users place in multimedia content. Unlike executable files, videos are generally considered safe, leading users to lower their guard. The sophistication of these viruses varies, with some capable of stealing personal information, encrypting files for ransom, or adding the infected device to a botnet. The threat is not just theoretical; incidents of malware distribution through video files have been documented, underscoring the importance of vigilance and the use of reputable antivirus software.
Exploits in Video Playback Software
Another significant risk comes from exploits in video playback software. Hackers can discover vulnerabilities in these programs and craft video files specifically designed to trigger these exploits. When played, the video activates the exploit, allowing attackers to execute malicious code on the user’s device. This can lead to unauthorized access, data theft, or further malware infection. The complexity of modern video playback software, which supports a wide range of codecs and formats, increases the potential attack surface. Manufacturers regularly release patches and updates to address these vulnerabilities, but users must be proactive in applying these fixes to protect themselves.
Both of these risks highlight the necessity for users to be cautious with the video content they choose to download and watch, especially from unverified sources. Using updated antivirus solutions, keeping software up to date, and preferring streaming content from reputable platforms can significantly reduce these risks.